Introduction to Application Security
Application security, also known as AppSec (from Application Security), is the combination of tools and practices aimed at identifying, fixing, and preventing vulnerabilities throughout the entire application development lifecycle—from initial design, development, deployment, and maintenance to eventual decommissioning.
Why Application Security is Important
Applications transmit, store, and process large amounts of sensitive data, ranging from personally identifiable information (PII) to intellectual property.
The proliferation of interconnected devices, cloud computing, and the Internet of Things (IoT) has expanded the attack surface for cybercriminals. Applications act as gateways to valuable data and resources, making them prime targets for exploitation. Attackers could gain access, modify, or delete sensitive or proprietary data, leading to severe consequences, including unauthorized access, data exfiltration, and service disruptions.
Additionally, the complexity of modern software architectures, such as microservices and containerization, introduces new levels of risk, making it challenging to maintain a comprehensive security approach.
This is why a holistic approach to application security is not only about protecting the application itself but also about ensuring a secure environment in which the application can operate. This involves securing the databases that the application interacts with, ensuring the security of the data it manages, and maintaining the integrity of the application’s code.
Objective of Application Security
The goal of application security is to ensure that software applications are secure and can withstand attacks from malicious actors, minimizing the likelihood of a successful breach. It is essential for ensuring operational continuity and providing reliable user experiences.
State of Application Security: Data and Statistics
Below are some of the latest statistics on application security, reflecting the current trends in this critical area of cybersecurity.
The burden of security debt continues to weigh heavily on software development. Over 70% of organizations have security debt, and nearly half have critical security debt. Security debt affects organizations of all sizes and stems from both original code and third-party code. (State of Software Security – Veracode)
The Verizon 2024 report highlighted a significant increase in attacks leveraging vulnerability exploitation as an entry point for breaches compared to previous years. The occurrence of such attacks has nearly tripled (a 180% increase) from 2023, largely due to incidents like MOVEit and similar zero-day vulnerabilities. These attacks were primarily leveraged by ransomware groups and other threat actors engaged in financial extortion. The primary vector for these initial breach points has been web applications.
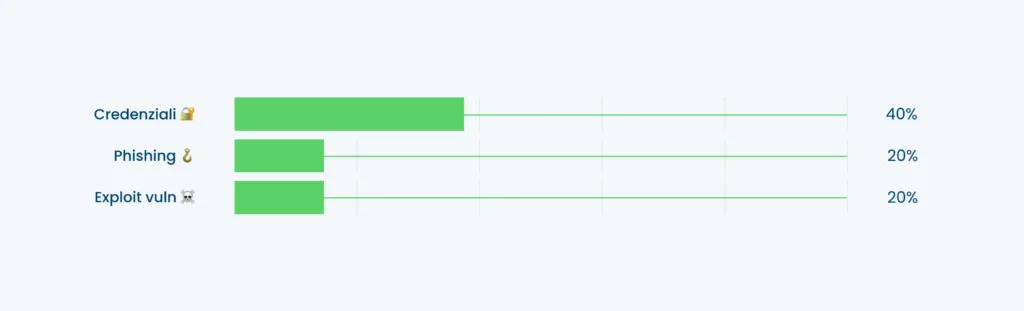
According to the Clusit 2024 Report, attacks exploiting application vulnerabilities constitute a significant portion of the cybersecurity threat landscape. Specifically, the analysis shows that 18% of global attacks in 2023 were carried out by exploiting application vulnerabilities. This figure represents a 76% increase compared to the previous year, underscoring how software and application vulnerabilities remain a primary target for cybercriminals.
Attacks exploiting these vulnerabilities can lead to severe consequences, including unauthorized access, data exfiltration, and service disruptions. The growing complexity of threats calls for stronger security measures and a greater focus on vulnerability management throughout the development and maintenance phases of applications.
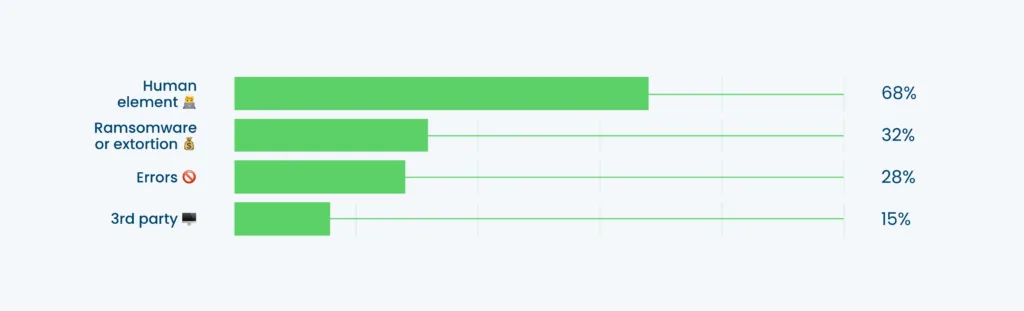
Statistics also indicate a rise in supply chain attacks, driven by organizations’ increasing reliance on third-party vendors. Verizon reports a 15% increase in supply chain attacks in 2024—a 68% increase compared to the previous year—primarily fueled by the use of zero-day exploits in ransomware and extortion attacks.
These attacks occur when a hacker infiltrates a system through an external partner or service provider with system access. The rise of such attacks has been attributed to their effectiveness and the difficulty in detecting them. This trend highlights the need for companies to thoroughly assess their vendors and implement robust security measures.
The reports on the state of application security mentioned above demonstrate that application and software vulnerabilities remain among the most common external attack vectors, along with software supply chain breaches.
Discover how we can help you
Together, we’ll find the best solutions to tackle the challenges your business faces every day.


