Cyber Threat Intelligence
Rely on our structured approach to manage Cyber Threat Intelligence activities, reducing risks and improving the efficiency of your response to emerging threats.
What is Cyber Threat Intelligence?
Cyber Threat Intelligence (CTI) is the collection and application of the most relevant and timely information to detect and respond to cybersecurity threats.
CTI provides insights into ongoing and emerging threats, as well as the tactics, techniques, and procedures (TTPs) of adversaries and vulnerabilities in their systems.
Our services
Our CTI services are tailored to the specific needs of your organization, with the goal of detecting and responding to cybersecurity threats effectively.
How we operate
Our Cyber Threat Intelligence services follow a continuous cycle to ensure ongoing improvements and adaptations. By leveraging multiple sources, we provide a comprehensive and in-depth view of emerging and ongoing threats.
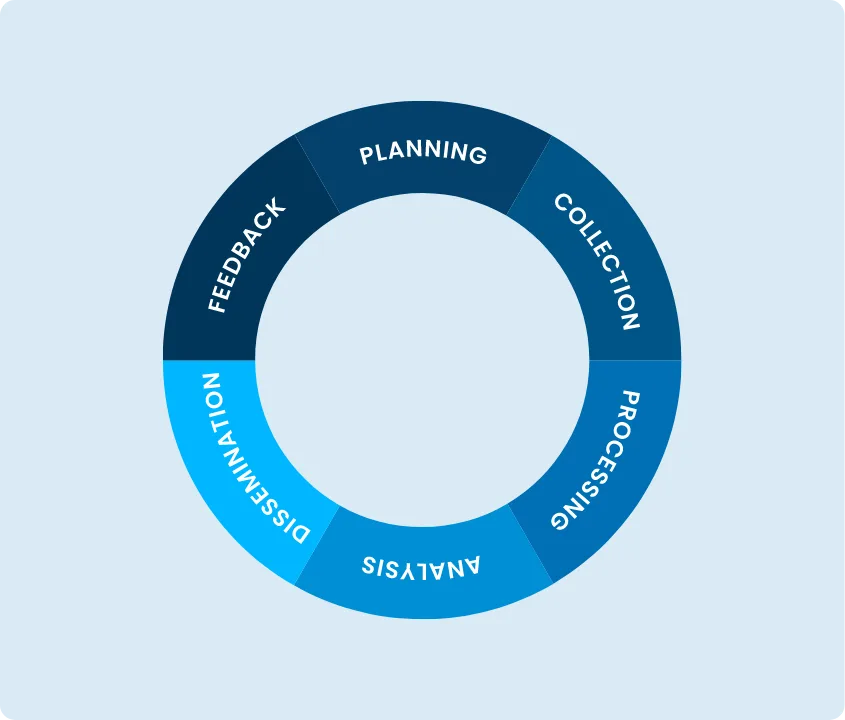
We follow the 6 phases of the CTI cycle
Our CTI operations follow a six-phase cyclic process that transforms raw data into strategic insights for the organization.
- Planning: Establishes the objectives and priorities for data collection.
- Collection: Gathers data from a variety of internal and external sources.
- Processing: Filters and formats data for analysis.
- Analysis: Interprets and analyzes processed data to identify specific threats and risks.
- Dissemination: Shares information and ensures decisions are based on up-to-date and reliable intelligence.
- Feedback: Evaluates the process’s effectiveness, making continuous improvements and adaptations.
We leverage data intelligence sources
Our CTI services draw from a diverse range of sources, including:
- Open Sources (OSINT)
- Technical Sources
- Human Sources (HUMINT)
- Internal Sources
- Commercial Sources
- Internal Intelligence
- Dark Web
- Social Media and Messaging Services

The benefits
Discover how we can help you strengthen
the security of your applications.
Contact us today to receive a free application check